Version 2.0, https://aasj.basyx-enterprise.net
2026-02
This specification defines the AAS JSON (AASJ) Exchange Package Format as an alternative to the AASX format specified in IDTA-01005. The AASJ format prioritizes simplicity, debuggability, and flexible security while maintaining full compatibility with Asset Administration Shell data models.
The following documents are referred to in the text in such a way that some or all of their content constitutes requirements of this document:
| Term | Definition |
|---|---|
| Identifiable | An AAS element with a globally unique identifier (Shell, Submodel, ConceptDescription) |
| Binary Content | Supplementary file referenced by an Identifiable (thumbnail, attachment) |
| Binary Reference | Pointer to existing Binary Content for deduplication |
| Content Hash | SHA-256 hash of file content for integrity verification |
| JWS | JSON Web Signature providing cryptographic authenticity |
| Package Metadata | Index file (metadata.json) containing package structure |
AAS JSON (AASJ) Exchange Package File Format Specification © 2026 by objective partner is licensed under CC BY 4.0. To view a copy of this license, visit https://creativecommons.org/licenses/by/4.0/
The AASJ package SHALL use the ZIP archive format as specified in the .ZIP File Format Specification.
*.aasjThe package SHALL contain files organized in a flat structure at the root level:
| File Pattern | Cardinality | Description |
|---|---|---|
metadata.json |
1..1 | Package metadata and index (mandatory) |
shell-{hash} |
0..* | Asset Administration Shell files |
submodel-{hash} |
0..* | Submodel files |
concept_description-{hash} |
0..* | Concept Description files |
binary-{hash} |
0..* | Binary attachment files |
The package MAY contain fully signed content (with JWS), but in that case it also MUST contain the decoded content as listed above.
| File Pattern | Cardinality | Description |
|---|---|---|
shell-{hash}.jws |
0..* | Asset Administration Shell files as embedded JWS |
submodel-{hash}.jws |
0..* | Submodel files as embedded JWS |
concept_description-{hash}.jws |
0..* | Concept Description files as embedded JWS |
binary-{hash}.jws |
0..* | Binary attachment files as embedded JWS |
File paths SHALL be generated using the following algorithm:
path = type + "-" + SHA256(identifier [+ reference])Where: - type in {shell,
submodel, concept_description,
binary} - identifier = Identifiable.id value -
reference = idShort path or “thumbnail” (binary files
only)
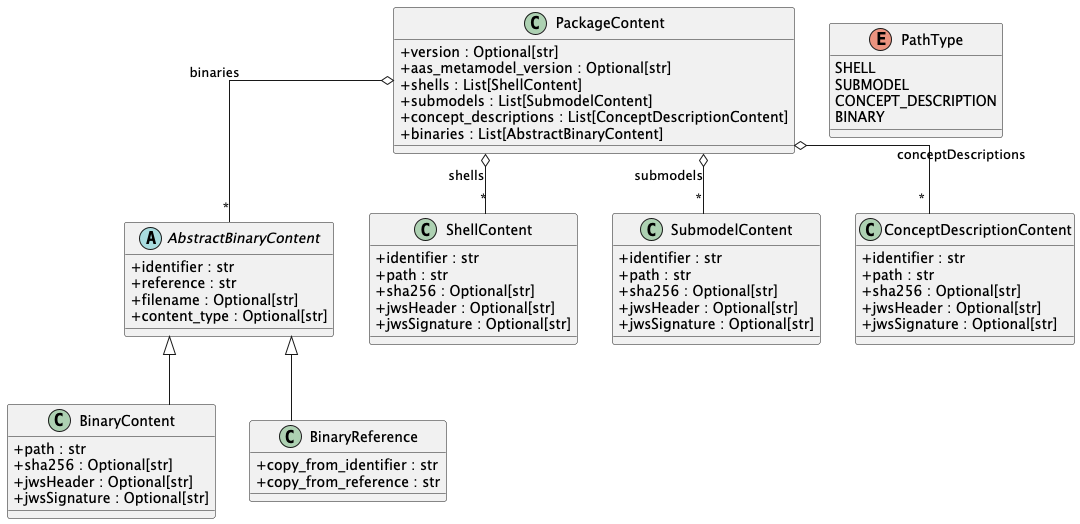
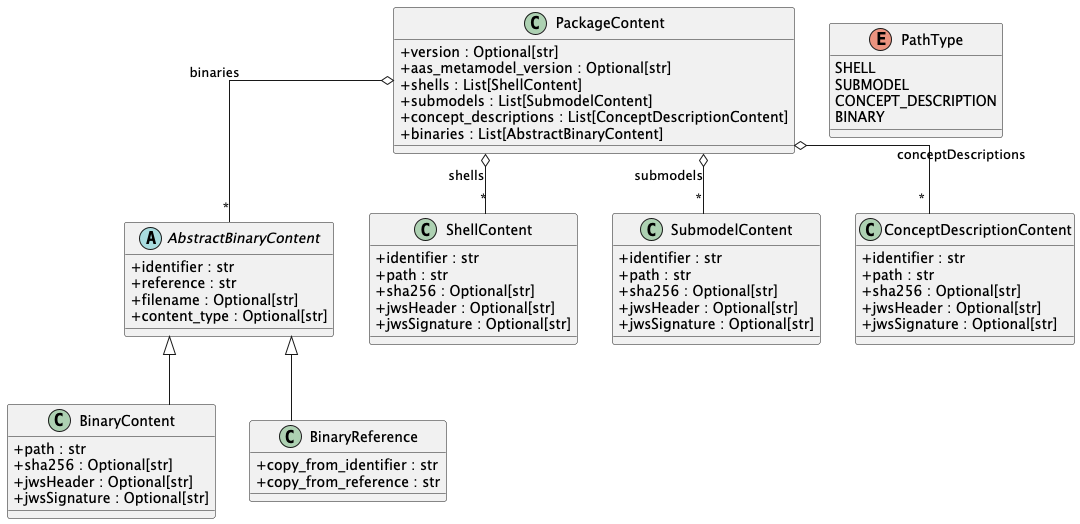
The metadata.json file SHALL contain a JSON object with
the following top-level fields:
| Field | Type | Cardinality | Description |
|---|---|---|---|
version |
string | 0..1 | Package format version (“1” or “2”) |
aasMetamodelVersion |
string | 0..1 | AAS metamodel version (default: “3.0”) |
shells |
array | 1..1 | Array of ShellContent objects |
submodels |
array | 1..1 | Array of SubmodelContent objects |
conceptDescriptions |
array | 1..1 | Array of ConceptDescriptionContent objects |
binaries |
array | 1..1 | Array of BinaryContent or BinaryReference objects |
| Field | Type | Cardinality | Version | Description |
|---|---|---|---|---|
identifier |
string | 1..1 | 1,2 | Shell identifier (IRI/URI) |
path |
string | 1..1 | 1,2 | File path within archive |
sha256 |
string | 0..1* | 2 | SHA-256 hash of content |
jwsHeader |
string | 0..1** | 2 | Base64url-encoded JWS header |
jwsSignature |
string | 0..1** | 2 | Base64url-encoded JWS signature |
jwsAttached |
boolean | 0..1 | 2 | Flag if redundant JWS file is included, default = false |
*Required if jwsHeader or jwsSignature present **Ether both or neither must be present
| Field | Type | Cardinality | Version | Description |
|---|---|---|---|---|
identifier |
string | 1..1 | 1,2 | Submodel identifier (IRI/URI) |
path |
string | 1..1 | 1,2 | File path within archive |
sha256 |
string | 0..1* | 2 | SHA-256 hash of content |
jwsHeader |
string | 0..1** | 2 | Base64url-encoded JWS header |
jwsSignature |
string | 0..1** | 2 | Base64url-encoded JWS signature |
jwsAttached |
boolean | 0..1 | 2 | Flag if redundant JWS file is included, default = false |
*Required if jwsHeader or jwsSignature present **Ether both or neither must be present
| Field | Type | Cardinality | Version | Description |
|---|---|---|---|---|
identifier |
string | 1..1 | 1,2 | ConceptDescription identifier |
path |
string | 1..1 | 1,2 | File path within archive |
sha256 |
string | 0..1* | 2 | SHA-256 hash of content |
jwsHeader |
string | 0..1** | 2 | Base64url-encoded JWS header |
jwsSignature |
string | 0..1** | 2 | Base64url-encoded JWS signature |
jwsAttached |
boolean | 0..1 | 2 | Flag if redundant JWS file is included, default = false |
*Required if jwsHeader or jwsSignature present **Ether both or neither must be present
| Field | Type | Cardinality | Version | Description |
|---|---|---|---|---|
identifier |
string | 1..1 | 1,2 | Parent Identifiable identifier |
reference |
string | 1..1 | 1,2 | Reference path within parent |
path |
string | 1..1 | 1,2 | File path within archive |
filename |
string | 0..1 | 2 | Original filename |
contentType |
string | 0..1 | 2 | MIME type |
sha256 |
string | 0..1* | 2 | SHA-256 hash of content |
jwsHeader |
string | 0..1** | 2 | Base64url-encoded JWS header |
jwsSignature |
string | 0..1** | 2 | Base64url-encoded JWS signature |
jwsAttached |
boolean | 0..1 | 2 | Flag if redundant JWS file is included, default = false |
*Required if jwsHeader or jwsSignature present **Ether both or neither must be present
| Field | Type | Cardinality | Version | Description |
|---|---|---|---|---|
identifier |
string | 1..1 | 2 | Target Identifiable identifier |
reference |
string | 1..1 | 2 | Target reference path |
copy_from_identifier |
string | 1..1 | 2 | Source Identifiable identifier |
copy_from_reference |
string | 1..1 | 2 | Source reference path |
filename |
string | 0..1 | 2 | Original filename (inherited) |
contentType |
string | 0..1 | 2 | MIME type (inherited) |
Files containing Identifiables (Shells, Submodels, ConceptDescriptions) SHALL:
Binary files SHALL:
The package format SHALL support four security tiers:
| Tier | SHA256 | JWS | Use Case |
|---|---|---|---|
| 0 | Optional | No | Legacy compatibility, trusted environments |
| 1 | Required | No | Basic integrity verification |
| 2 | Required | Required | Full cryptographic validation |
| 3 | Required | Required | Full cryptographic validation without logic |
When SHA256 hashes are used:
When JWS signatures are used:
For signed content, the following process SHALL be applied:
Export (Signing): 1. Obtain JWS with embedded
payload from signing service 2. Split JWS at period delimiters:
header.payload.signature 3. Store base64url-decoded payload
as file content 4. Store header in jwsHeader field 5. Store signature in
jwsSignature field 6. Compute and store SHA256 of decoded payload 7.
Optionally include redundant .jws file and set jwsAttached to true
Import (Validation) - jwsAttached is false: 1.
Verify SHA256 hash of file content 2. Base64url-encode file content to
recreate payload. ATTENTION: Pure byte processing must be used
to avoid byte manipulation by any string / text / JSON processing. 3.
Reconstruct JWS: {jwsHeader}.{payload}.{jwsSignature} 4.
Validate signature using appropriate algorithm and key
Import (Validation) - jwsAttached is true: 1. Validate signature using appropriate algorithm and key
| Version | Identification Criteria |
|---|---|
| 1 | version absent or “1”, no security fields |
| 2 | version = “2”, security fields optional |
Version 1 readers: - SHALL ignore unknown fields in metadata.json - SHALL process content files normally - SHALL NOT validate security fields
Version 2 readers: - SHALL process Version 1 packages - SHALL apply security validation when fields present - MAY upgrade Version 1 packages to Version 2
Version 1 to Version 2: 1. Set version
to “2” 2. Add aasMetamodelVersion, default is “3.0” 3.
Optionally compute sha256 for content 4. Optionally add
filename/contentType to binaries
The package format addresses these security concerns:
| Threat | Mitigation | Security Tier |
|---|---|---|
| Content tampering | SHA256 hash validation | 1, 2 |
| Origin spoofing | JWS signature validation | 2 |
| Replay attacks | Timestamp validation in JWS | 2 |
| Information disclosure | ZIP encryption (optional) | All |
| Resource exhaustion | Size limits, streaming | All |
| Class | Requirements |
|---|---|
| Producer-Basic | Generate valid Version 1 packages |
| Producer-Standard | Generate Version 2 packages with SHA256 |
| Producer-Full | Generate Version 2 packages with JWS |
| Consumer-Basic | Read Version 1 packages |
| Consumer-Standard | Read Version 2, validate SHA256 |
| Consumer-Full | Read Version 2, validate JWS |
{
"version": "2",
"aasMetamodelVersion": "3.0",
"shells": [
{
"identifier": "https://example.com/aas/123",
"path": "shell-c51b17f0c6525f4e81843ccd438cc77f70df39113530fc87182027b400de1ac3",
"sha256": "a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890",
"jwsHeader": "eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9",
"jwsSignature": "SflKxwRJSMeKKF2QT4fwpMeJf36POk",
"jwsAttached": false
}
],
"submodels": [
{
"identifier": "https://example.com/sm/456",
"path": "submodel-c1e09905a53cdcf8e2e5aa0a2335b4f9e3f3a921ca0e438d4cef8ec58c5162bc",
"sha256": "b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1"
}
],
"conceptDescriptions": [],
"binaries": [
{
"identifier": "https://example.com/aas/123",
"reference": "thumbnail",
"path": "binary-a7814558759e609ab85d4ff296f7cebd2c71aae5e1fa848a25593057bbaaf830",
"filename": "thumbnail.png",
"contentType": "image/png",
"sha256": "c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2"
},
{
"identifier": "https://example.com/sm/456",
"reference": "Documents[7].DocumentVersions[0].PreviewFile",
"path": "binary-65c4166574278e6eebf24bbb8d55aafa655f8b6a963301cfef3bccba3290d961",
"filename": "preview.pdf",
"contentType": "application/pdf",
"sha256": "d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3"
}
]
}Shell
https://example.com/aas/123shell-c51b17f0c6525f4e81843ccd438cc77f70df39113530fc87182027b400de1ac3Submodel
https://example.com/sm/456submodel-c1e09905a53cdcf8e2e5aa0a2335b4f9e3f3a921ca0e438d4cef8ec58c5162bcBinary (Thumbnail)
https://example.com/aas/123thumbnailbinary-a7814558759e609ab85d4ff296f7cebd2c71aae5e1fa848a25593057bbaaf830Binary (Submodel Attachment)
https://example.com/sm/456Documents[7].DocumentVersions[0].PreviewFilebinary-65c4166574278e6eebf24bbb8d55aafa655f8b6a963301cfef3bccba3290d961{
"identifier": "https://example.com/aas/123",
"path": "shell-c51b17f0c6525f4e81843ccd438cc77f70df39113530fc87182027b400de1ac3"
}{
"identifier": "https://example.com/aas/123",
"path": "shell-c51b17f0c6525f4e81843ccd438cc77f70df39113530fc87182027b400de1ac3",
"sha256": "a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890"
}{
"identifier": "https://example.com/aas/123",
"path": "shell-c51b17f0c6525f4e81843ccd438cc77f70df39113530fc87182027b400de1ac3",
"sha256": "a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890",
"jwsHeader": "eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9",
"jwsSignature": "SflKxwRJSMeKKF2QT4fwpMeJf36POk",
"jwsAttached": false
}{
"identifier": "https://example.com/aas/123",
"path": "shell-c51b17f0c6525f4e81843ccd438cc77f70df39113530fc87182027b400de1ac3",
"sha256": "a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890",
"jwsHeader": "eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9",
"jwsSignature": "SflKxwRJSMeKKF2QT4fwpMeJf36POk",
"jwsAttached": true
}Implicit path for redundant JWS file:
shell-c51b17f0c6525f4e81843ccd438cc77f70df39113530fc87182027b400de1ac3.jws
{
"identifier": "https://example.com/aas/123",
"reference": "thumbnail",
"path": "binary-a7814558759e609ab85d4ff296f7cebd2c71aae5e1fa848a25593057bbaaf830",
"filename": "thumbnail.png",
"contentType": "image/png",
"sha256": "c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2"
}{
"identifier": "https://example.com/sm/456",
"reference": "Documents[7].DocumentVersions[0].PreviewFile",
"path": "binary-65c4166574278e6eebf24bbb8d55aafa655f8b6a963301cfef3bccba3290d961",
"filename": "preview.pdf",
"contentType": "application/pdf",
"sha256": "d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3d4e5f67890a1b2c3"
}